Critical Security Alert: Vulnerability in pac4j-jwt Library
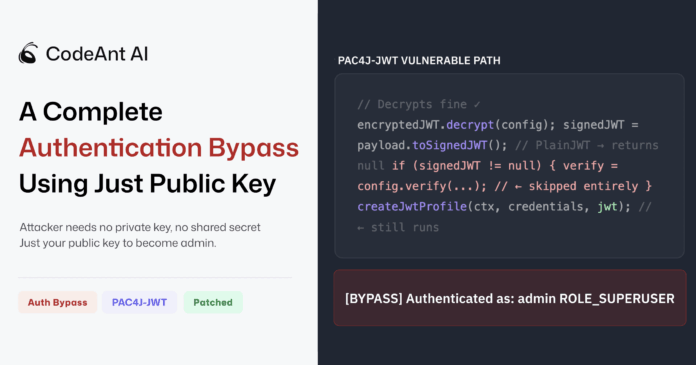
A severe security flaw has been discovered in the widely-used pac4j-jwt Java authentication library, identified as CVE-2026-29000 with a CVSS score of 10.0. This vulnerability can lead to a complete authentication bypass, allowing attackers to impersonate any user—including admins—using only the server’s RSA public key.
Key Insights:
- Nature of the Flaw: An anomaly in signature verification can cause it to be silently skipped, enabling exploitation.
- Patch Availability: Quick action was taken—maintainer Jérôme Leleu confirmed and published patches:
- Upgrade to:
- 4.x: 4.5.9 or newer
- 5.x: 5.7.9 or newer
- 6.x: 6.3.3 or newer
- Upgrade to:
- Research Foundation: CodeAnt AI examined patch effectiveness post-CVE disclosure and found critical vulnerabilities.
Is your system at risk? Ensure you check and update your version immediately.
🔗 Let’s foster a secure tech community; share this alert and keep your network safe!