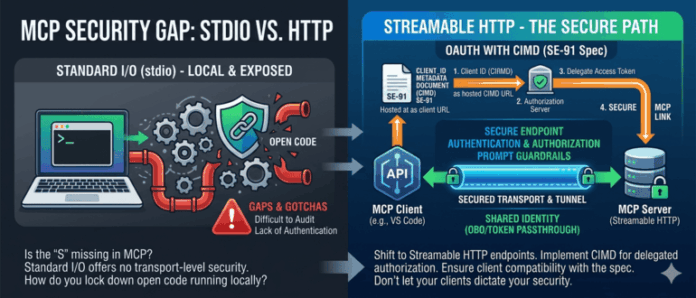
The Model Context Protocol (MCP) ecosystem is developing, particularly in terms of security. Despite a humorous notion that “S” stands for security in MCP, significant gaps exist. Key transport methods include standard input/output (stdio) and streamable HTTP. Securing an MCP server resembles installing a third-party package; however, local code security remains complex. Streamable HTTP is preferred as it offers endpoints that can be secured through AI-specific gateway solutions, enabling authentication and authorization controls. Authentication and authorization in MCP are critical, using OAuth frameworks for delegated access. The Client ID Metadata Documents (CIMD) protocol is gaining traction, but compatibility across different clients can complicate the OAuth flow. Users must ensure their clients support specific OAuth specifications, particularly for OIDC, as inconsistencies can arise. The takeaway is to thoroughly test OAuth flows across multiple clients and stay updated on MCP security developments. Consistent testing ensures robust security across varied environments.
Source link
Share
Read more