🚨 The Axios Attack: A Cautionary Tale for AI Developers 🚨
On March 31, 2026, a serious breach rocked the npm ecosystem when a DPRK-linked attacker published a backdoored version of the popular package axios.
Key Details:
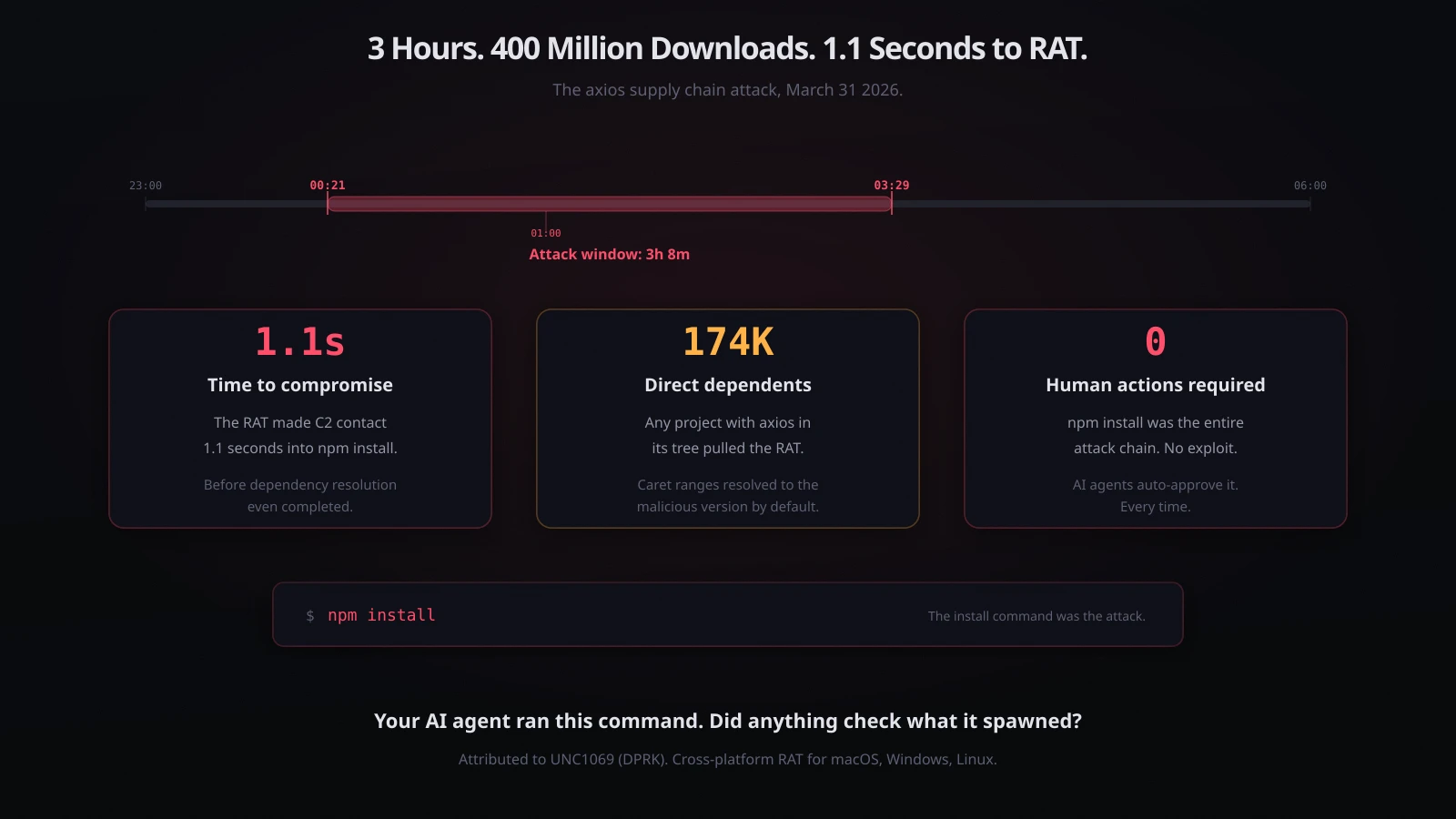
- Attack Window: 3 hours and 8 minutes.
- Execution Time: 1.1 seconds post
npm install. - Impact: Included a Remote Access Trojan (RAT) for macOS, Windows, and Linux, executed autonomously without user action.
Understanding the Attack:
- Attack Vector: Compromised maintainer account led to publishing malicious versions.
- AI Coding Agents: Run
npm installroutinely, leading to unmonitored execution of malicious scripts. - Consequences: Every installation during the attack window pulled the RAT into systems indiscriminately.
Next Steps for Developers:
- Check lockfiles for malicious versions of axios.
- Look for RAT artifacts in system directories.
- Rotate credentials if affected.
- Pin axios to safe versions to prevent future exploits.
What This Means:
The Axios attack exemplifies the urgent need for enhanced security measures in AI environments. As developers, we must recognize that automated commands aren’t as routine as they appear.
🔗 Join the conversation on safeguarding our tech ecosystem! Share your thoughts below!